Several days ago a document from the corporation Zerofox was leaked on the internet. Zerofox is a domestic spying organization there is no other word for them. They are paid obscene amounts of money to monitor people's Twitter and Facebook accounts, and provide the results of their stalking to police departments and other people who are in theory bound to respect the autonomy of free political speech. In the document that was leaked, Zerofox claimed to have "mitigated" 19 "threats" and "monitored" hundreds of others. The document is available here.
What constitutes a threat? Political speech that is critical of the police. At the top of the list of "physical threats" are #blacklivesmatter activists Deeray McKesson and Johnetta Elzie, neither of whom have ever been convicted of a violent crime AFAICT. The report recommends that police engage in "continuous monitoring" of the pair and justify this absurd response because they have "coordinated protests". The two were not alone on the list, which lists several other protesters and bloggers. Several times Zerofox recommended police perform a social media "profile takedown"; one of these recommendations was justified by Zerofox because an individual "slandered" a police officer. The slander consisted of taking screenshots of the police officer's Facebook posts - posts that included long, rambling racist screeds.
Most of this is well known, or will be over the next couple of days. This is a tech website! So what is my angle?
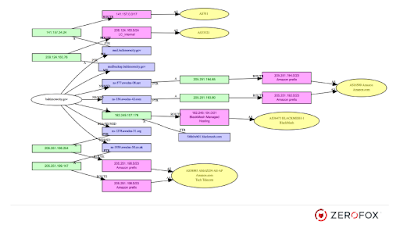
After the first few pages of creepy Stasi-style investigation, the report began to list what Zerofox believed were vulnerabilities in City of Baltimore networks. The "vulnerability reports" are laughably amateurish and consist almost entirely of information available from WHOIS, googling lists of applications combined with the word "exploit" and maybe nmap scans.
There are two things about this report that are interesting. First of all, it includes a list of Baltimore city online resources that would not immediately be publicly available - servers like email backups and an Exchange server that is either entirely for internal use or horrifically misconfigured (it lacks an rDNS entry, so it won't be doing a lot of sending to email servers setup by grown-ups).
And secondly, I really can't stress enough how bottom of the barrel this is. Let's just set aside the first part of this product that the people of Baltimore were forced to purchase. If this is what municipal governments believe infosec looks like, we are in for quite a few more repeats of Office of Personnel Management "cyber-warfare Pearl Harbors".
(Did you just vomit a little? I always vomit a little when I hear anything that begins with the prefix "cyber-")
What constitutes a threat? Political speech that is critical of the police. At the top of the list of "physical threats" are #blacklivesmatter activists Deeray McKesson and Johnetta Elzie, neither of whom have ever been convicted of a violent crime AFAICT. The report recommends that police engage in "continuous monitoring" of the pair and justify this absurd response because they have "coordinated protests". The two were not alone on the list, which lists several other protesters and bloggers. Several times Zerofox recommended police perform a social media "profile takedown"; one of these recommendations was justified by Zerofox because an individual "slandered" a police officer. The slander consisted of taking screenshots of the police officer's Facebook posts - posts that included long, rambling racist screeds.
Most of this is well known, or will be over the next couple of days. This is a tech website! So what is my angle?
After the first few pages of creepy Stasi-style investigation, the report began to list what Zerofox believed were vulnerabilities in City of Baltimore networks. The "vulnerability reports" are laughably amateurish and consist almost entirely of information available from WHOIS, googling lists of applications combined with the word "exploit" and maybe nmap scans.
 |
| 2 kilos of WHOIS; street value $250,000 |
(Did you just vomit a little? I always vomit a little when I hear anything that begins with the prefix "cyber-")
